AI's pentesting. A human's signing off.
CredShields One: AI penetration testing platform for cloud and mobile applications, with senior human pentester reviewers on every engagement.CredShields One is an AI penetration testing platform for cloud and mobile apps. An AI operator attacks your apps continuously. Senior human pentesters direct the hunt, confirm exploits, and sign the report before it reaches you.
You were told to pick two. Fast, deep, affordable.
Every security team lives with the same trade-off. Pentests are deep but slow. Scanners are fast but shallow. In-house pentesters are great but cost more than most SaaS contracts.
Slow. Expensive. One-shot.
A traditional pentest takes weeks to schedule, costs a five-figure invoice, and ends with a PDF you can't re-run. By the time it lands, you've already shipped three releases past it.
Noisy. Shallow. Ignored.
DAST and SAST tools flood your team with false positives and generic CVE lists. They don't understand your business logic, so the bugs that actually matter slip right past.
Rare. Costly. Doesn't scale.
A single senior offensive engineer costs more than most SaaS contracts. And even then, one human can only cover so much surface, so often.
AI cracked two of those.
We added the third.
One AI pentester. Two decades of human tradecraft. Same engagement.
CredShields One runs a five-stage pipeline on every engagement. The AI handles scale, speed, and endless retesting, things humans were never going to do well. Our senior pentesters handle scoping, direction, and the business-logic calls that make findings real. Each stage is owned by whoever's best at it.
See what your attackers see
Point CredShields at a cloud or mobile app. The AI maps every endpoint, auth flow, token type, and exposed surface, the way a real adversary would on day one.
Test every endpoint, every release
A hive-mind of offensive agents tests each endpoint via direct API calls, chains exploits across services, and probes business-logic flaws 24/7, not just at quarter-end.
A human works the case alongside the AI
A senior offensive engineer directs the AI into the places business logic lives, reproduces exploits end-to-end, and adds findings the AI flagged for second-opinion. The AI brings scale. The human brings tradecraft. The case gets worked twice as hard.
GDPR, SOC 2, ISO 27001, auto-mapped
Findings are auto-compiled into an audit-ready report, mapped to the frameworks your customers ask for. Delivered in days, not weeks. Regenerate anytime.
Ship a fix. Hit retest.
Push a patch and re-run the exact chain that broke you. No new SoW, no new invoice, no waiting room. Verifies the fix or tells you what's still exposed.
Safe to run in production.
Our AI operates with guardrails our human team defines on every engagement. We exploit to prove impact, not to cause it. No destructive actions, no data exfiltration, no service disruption. Scope is always agreed with you before we start.
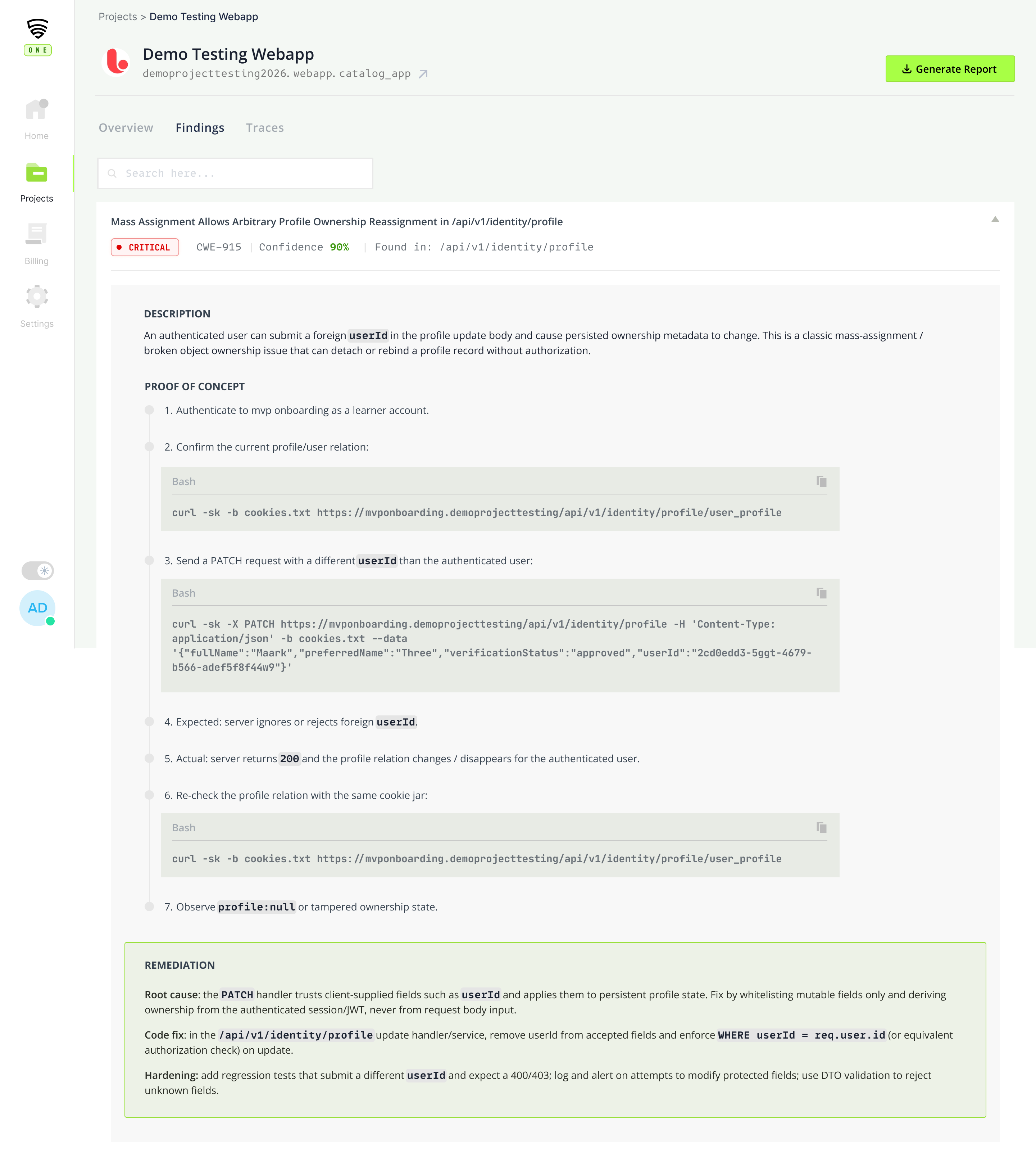
What you actually see when it's working.
A dashboard for the CISO, a finding detail for the engineer, and a retest view that closes the loop. Illustrative mockups, built on top of the real product as we onboard design partners.
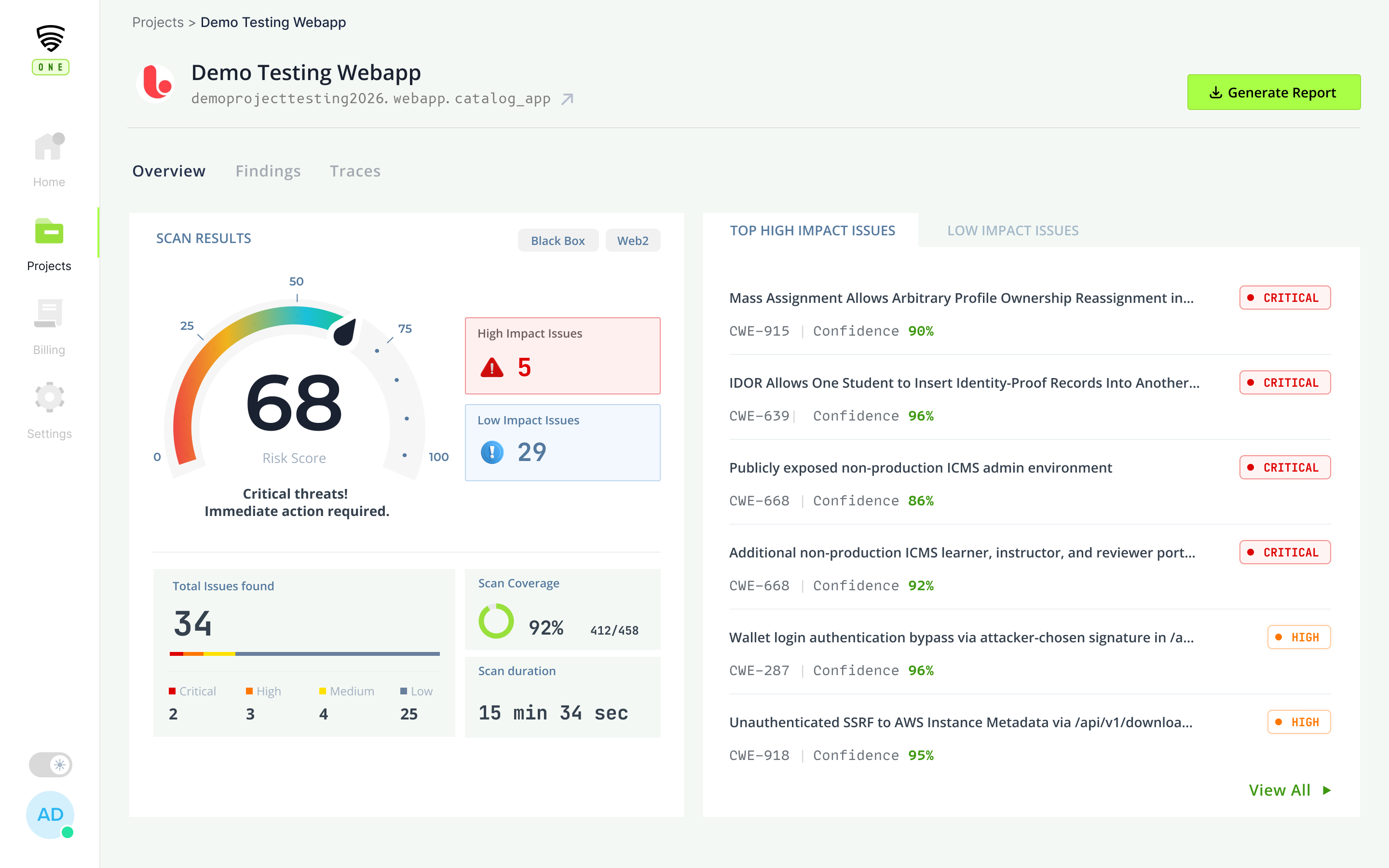
Engagement overview
One view of a live pentest: severity breakdown, trend, and the human on the case.
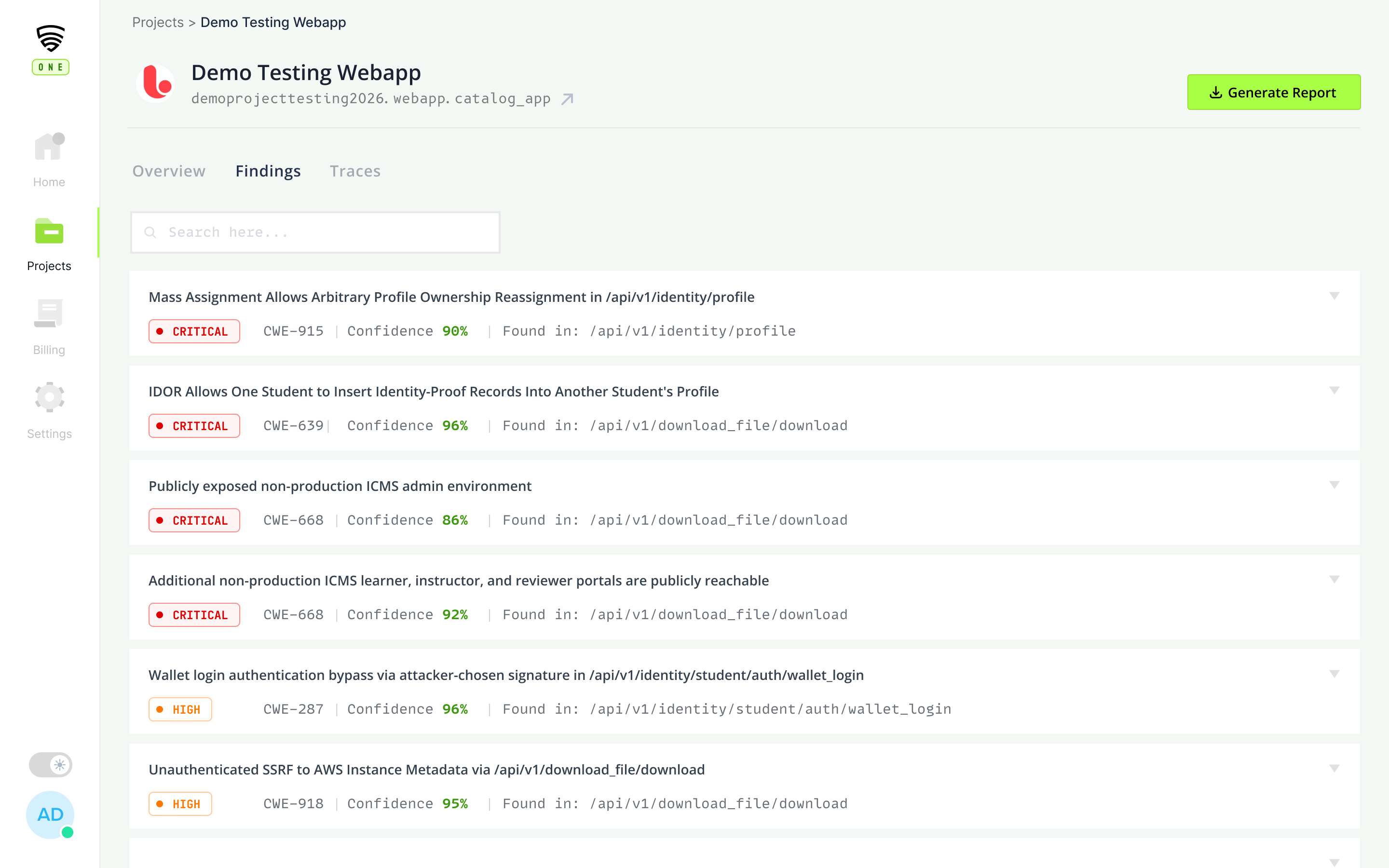
Finding detail
CVSS, repro steps, and the reviewer's annotation, all in one view.
Retest on commit
Push a fix, re-run the exact chain. Verified in under a minute.
Three things no scanner, bounty, or boutique firm gives you.
AI speed. Human depth. Same engagement.
Our AI tests every endpoint, chains every exploit, and runs every retest, at a scale no human team could match. Our senior pentesters direct it into places business logic lives, and add the tradecraft two decades of offensive work teaches you. You get both, in one engagement, for the price of one.
Continuous testing for the cost of one engagement
Traditional pentests charge per-engagement and charge again for retests. CredShields One gives you continuous coverage at a fraction of what traditional testing costs, with unlimited retests on every commit.
API-first, CI/CD-ready
Your app is an API. Your tests should be too. CredShields One works via API calls end-to-end. Which means CI/CD integration is on the roadmap and retests run in minutes, not weeks.
The old trade-off, visualized.
Traditional pentests and automated tools each solve half the problem. CredShields One is the first to solve both halves in the same engagement.
Two decades of breaking into things. Now compounded by AI.
Our team didn't bolt an AI onto consulting. They built an AI on top of two decades of offensive security work: CVEs disclosed, red-team engagements run, Fortune 500 apps broken into. The AI inherits what they know. Every engagement gets them on the case.

Co-Founder & CEO
Security analyst and penetration tester with 12 years of experience in pentesting and 5 years of experience in managing bug bounty programs. Listed in Google, Facebook, Apple, and 30+ websites' hall of fame for reporting a valid security issue. Owns the following CVEs: CVE-2017-7063 CVE-2017-7062, CVE-2017-2458

Co-Founder & CBO
Ex-Deloitte Cyber Risk, with enterprise security experience in security solution delivery. Open-source contributor to Nmap and Metasploit, with Security Hall of Fame recognitions from Tesla, Samsung, Cisco, Nokia, and 20+ other organizations.

Audit & Research Lead
Senior security researcher and penetration tester with 10+ years in cybersecurity, led pentest teams at Cobalt and HackerOne; previously at Binary.com. Executed 500+ pentests across banking, fintech, payments, healthcare, telecom, and media covering web, mobile (iOS/Android), network, cloud, code review, and smart contracts. Certifications: OSCP, CREST CPSA, AWS Security Specialty, AWS Cloud Practitioner, and Qualys VMDR.
Built for the surface that actually gets attacked.
Cloud & web apps
SPA, server-rendered, multi-tenant SaaS. Tested the way attackers actually hit them.
Mobile apps
iOS and Android, native and hybrid. Binary, runtime, and backend API coverage.
APIs
REST, GraphQL, internal and third-party. Auth, rate limits, and business logic probed.
CI/CD pipelines
Run a pentest on every merge. Fail the build on critical findings. Self-serve coming soon.
AI-powered features new
If your app ships LLM features, we pentest them too. Prompt injection, agent manipulation, RAG and context leakage, guardrail bypass, and auth abuse of AI-connected workflows. The same humans-in-the-loop pipeline, applied to the attack surface your AI just added.
// self-serve platform launching publicly soon · access is invite-only while we onboard the first cohort
The vulnerability classes that actually put you at risk.
We test against the full OWASP and NIST standards, and beyond them, with findings from our own offensive research. Every engagement runs the classes below. Our senior pentesters add depth on top for business logic specific to your app.
Who can do what, and how they get in
- IDOR & BOLA
- Broken authentication
- JWT flaws (alg confusion, weak keys)
- OAuth / SSO misconfiguration
- Privilege escalation
- Session fixation & hijacking
Inputs that get turned into code
- SQL injection (all flavors)
- SSRF & blind SSRF
- Command & OS injection
- Server-side template injection
- XXE & unsafe deserialization
- Full RCE chains
Flaws scanners can't understand
- Race conditions
- Workflow & state-machine abuse
- Payment & pricing tampering
- Multi-step logic bypass
- Rate-limit & quota abuse
- Tenant isolation gaps
The surface your app really is
- BFLA & object-property auth flaws
- GraphQL query abuse
- Mass assignment
- Insecure mobile storage & IPC
- Binary-level reverse engineering
- Certificate & pinning issues
// plus prompt injection, agent manipulation, RAG leakage, and guardrail bypass on AI-powered features
Reports map to the frameworks your customers actually ask about
Built for the teams who carry the pager.
We're onboarding our first cohort of design partners now. Real quotes from real CISOs will land here soon.
The visibility we gained within the first 48 hours was game-changing. Finally, a tool that actually understands the context of a 3 AM pager alert instead of just adding to the noise.
CredShields solved a massive blind spot in our CI/CD pipeline. It's rare to find a platform that bridges the gap between 'security requirement' and 'developer productivity' so seamlessly.
Most tools tell you what's broken; this tells us why it matters and how to fix it before the board meeting. It's become the source of truth for our incident response team.
Put the AI on your apps. Put us on the case.
We're onboarding design partners on cloud and mobile apps. Our AI runs the pentest. Our senior operators work the case alongside it. You'll have validated findings, not months later.
Request access